Recent Posts
7 Useful Home Appliance Care And Maintenance Tips – 2023 Guide
Let’s be honest, a wide range of home appliances have made our lives so much better and easier. In fact, most people wouldn’t be...
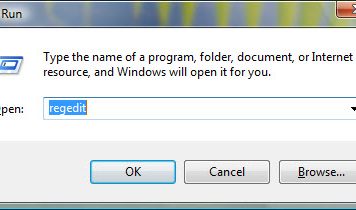
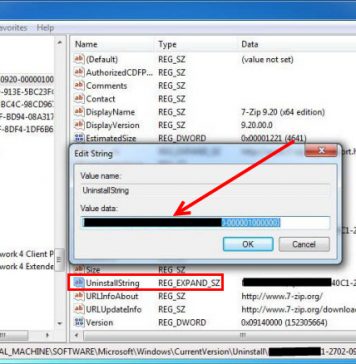
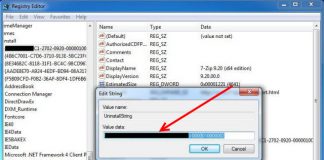
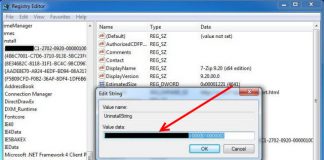
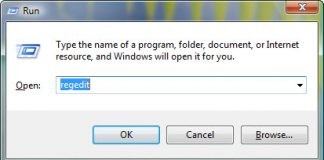
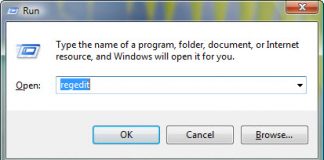
Uninstall and Remove AMD Step by Step 2023 Guide
Do you need to uninstall AMD OverDrive to fix some problems? Are you looking for an effective solution to completely delete all files from...
Uninstall and Remove BattlEye from OA Uninstall Step by Step 2023 Guide
Do you need to uninstall BattlEye for OA Uninstall to fix some issues? Are you looking for an effective solution to completely delete all...
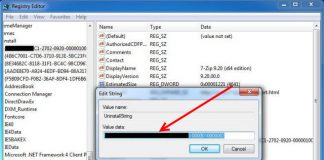
Uninstall and Delete BgInfo 4.16 Step by Step 2023 Guide
Do you need to delete BgInfo 4.16 to solve some problems? Are you looking for an effective solution to completely delete all files from...
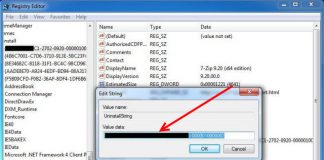
Uninstall and Remove Directx 11 Step by Step 2023 Guide
Do you need to uninstall Directx 11 to fix some problems? Are you looking for an effective solution to completely delete all files from...