When it comes to website development, the MySQL database is a crucial component that serves as the foundation for the majority of websites. However, with the rise of cybercrime and hacking attempts, webmasters need to take extra precautions to ensure their website’s security.
This is where basic pentest services come in handy as they help identify vulnerabilities and weaknesses in the system that could potentially be exploited by hostile hackers. In this tutorial, we will explore how penetration tests work specifically on the MySQL database, providing you with valuable insights on how to keep your website safe from potential threats.
The MySQL database serves as the foundation of the majority of websites. To guard against hostile hackers hacking into their website, every webmaster must undertake basic pentest services on the MySQL database. Let’s start our tutorial on how penetration tests work on the MySQL database.
Advantages of MySQL server penetration testing

Generally, a penetration test can be arranged for many things:
- APIs;
- IoT devices;
- networks;
- web applications;
- websites;
What’s common for all of these? They all function through servers, one way or another. This way, by testing the server’s security measures, you can ensure the basic level of cybersecurity in your digital environment.
The basics of MySQL server pen testing

Penetration testing simulates an assault on a system, network, or application with permission in order to identify potential security holes that might be exploited. Servers, operating systems, services, and application bugs, as well as inappropriate setups, can all have vulnerabilities.
No defense is unbreakable, of course. Your security posture will influence how quickly and how severely your resources can be hacked. An assailant faces more risk and a greater chance of being apprehended the longer he or she continues to try to breach your defenses.
As you can guess, the team of ethical (or “white”) hackers uses a series of MySQL injections and other hacking techniques to gain access to the server and explore its vulnerabilities for further reporting.
Your step-by-step guide

Understanding how penetration tests for servers are carried out is crucial since it is a challenging feat. The entire procedure has been broken down into a few distinct parts ‒ let’s examine each one individually.
The first step is reconnaissance. It involves collecting data about the target systems, such as IP addresses, operating systems, and code libraries.
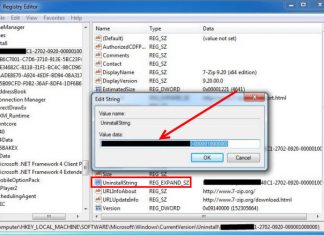
Next, a tester gains access to the targeted server. To do that, they need to determine whether the server is in their local or remote network. Also, they need to know the right port number. After that, credentials are collected to grant further access.
This is when the weaknesses can be fully explored: unnecessary database accesses and privileges, backdoors, and exploits. After the whole structure is revised, the penetration testing team starts the report creation.
The best pentest practices include figuring out the characters that can be prone to SQL injections, testing accesses and privileges, and checking the cloud storage’s security if the server is in the cloud.
These procedures can help businesses make sure that their servers and online apps are safe and secure.